AWS Account Setup
When adding an AWS account to the scheduler, you need to provide the appropriate permissions for the scheduler to perform it’s functions. We provide a simple cloudformation template you can deploy into your account that will deploy an IAM role + inline policy the scheduler can use.
Once the role has been deployed into your AWS account you need to make sure the account is configured.
- If the account is not added to the project, just add the account to the project
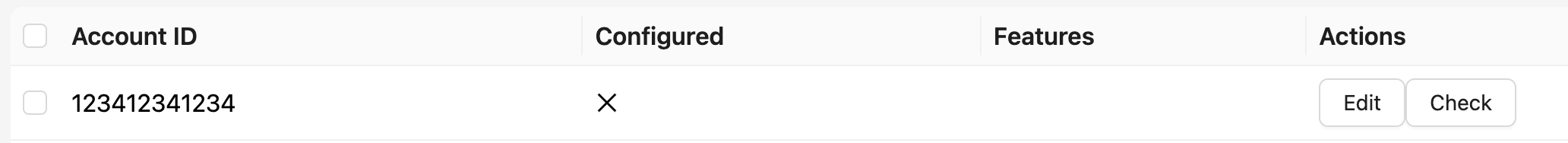
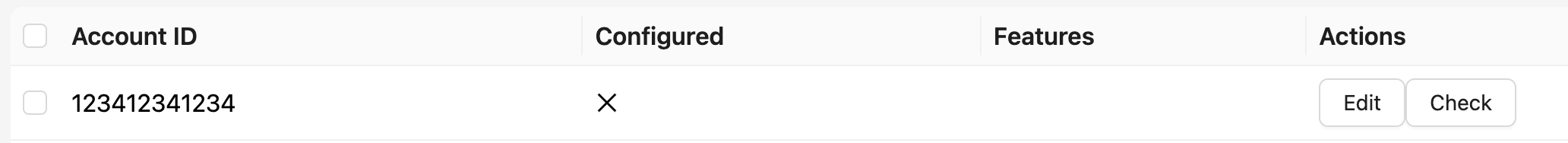
- If the account is already added to the project, click the ⋯ menu on the account row and select Test Connection in the accounts view shown below
Note
If you signed up through the AWS Marketplace, the account which you used will be added automatically to the scheduler. However, you still need to deploy the appropriate IAM role and inline policy for the scheduler and then use the Test Connection option from the ⋯ menu on the Accounts tab for the scheduler to function properly.
Template
Below is the template you can use to deploy an IAM role that gives permissions to the system to access resources in your account
AWSTemplateFormatVersion: 2010-09-09
Parameters:
ExternalId:
Type: String
Description: "External ID for secure cross-account access. Find this value at Tenant Management > Defaults tab in the SkySaver portal."
MinLength: 1
NoEcho: false
Resources:
SkySaverSolutionsIAM:
Type: 'AWS::IAM::Role'
Properties:
RoleName: 'SkySaverScheduler'
Path: "/"
Policies:
- PolicyName: MonitorPermissions
PolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: "Allow"
Sid: "lambdapermissions"
Resource:
- "*"
Action:
- "lambda:ListFunctions"
- "lambda:ListTags"
- "lambda:GetFunctionConcurrency"
- "lambda:GetProvisionedConcurrencyConfig"
- "lambda:ListVersionsByFunction"
- "lambda:PutFunctionConcurrency"
- "lambda:DeleteFunctionConcurrency"
- "lambda:ListProvisionedConcurrencyConfigs"
- "lambda:PutProvisionedConcurrencyConfig"
- Effect: "Allow"
Sid: "ec2permissions"
Resource:
- "*"
Action:
- "ec2:StartInstances"
- "ec2:StopInstances"
- "ec2:DescribeInstances"
- "ec2:ModifyInstanceAttribute"
- Effect: "Allow"
Sid: "enaborphanedsgfinderpermissions"
Resource:
- "*"
Action:
- "ec2:DescribeNetworkInterfaces"
- "ec2:DescribeSecurityGroups"
- Effect: "Allow"
Sid: "asgpermissions"
Resource:
- "*"
Action:
- "autoscaling:DescribeAutoScalingGroups"
- "autoscaling:DescribeTags"
- "autoscaling:UpdateAutoScalingGroup"
- Effect: "Allow"
Sid: "rdspermissions"
Resource:
- "*"
Action:
- "rds:DescribeDBClusters"
- "rds:DescribeDBInstances"
- "rds:StopDBCluster"
- "rds:StopDBInstance"
- "rds:StartDBInstance"
- "rds:StartDBCluster"
- "rds:ModifyDBCluster"
- "rds:ModifyDBInstance"
- Effect: "Allow"
Sid: "taggingperms"
Resource:
- "*"
Action:
- "tag:GetResources"
- Effect: "Allow"
Sid: "s3curpermissions"
Resource:
- "*"
Action:
- "s3:ListBucket"
- "s3:GetObject"
- "s3:GetBucketLocation"
- Effect: "Allow"
Sid: "costexplorerpermissions"
Resource:
- "*"
Action:
- "ce:GetRightsizingRecommendation"
- "ce:GetCostAndUsage"
- "ce:GetSavingsPlansPurchaseRecommendation"
- "ce:GetReservationPurchaseRecommendation"
- Effect: "Allow"
Sid: "s3intelligenttiering"
Resource:
- "*"
Action:
- "s3:ListAllMyBuckets"
- "s3:GetBucketLocation"
- "s3:GetLifecycleConfiguration"
- "s3:PutLifecycleConfiguration"
- "s3:GetBucketTagging"
- "s3:PutIntelligentTieringConfiguration"
AssumeRolePolicyDocument:
Version: "2012-10-17"
Statement:
- Effect: "Allow"
Principal:
AWS: "arn:aws:iam::975050237171:root"
Action:
- "sts:AssumeRole"
Condition:
StringEquals:
sts:ExternalId: !Ref ExternalIdUsage Instructions
- Deployment: Deploy the template in your AWS account using the AWS CloudFormation console or CLI. This will create the
SkySaverSchedulerIAM role with all necessary permissions. - Role Assumption: After deployment, the system will assume this role to access and manage AWS resources in your account.
Deploying The CloudFormation Template
We have created a step by step walkthrough for deploying our provided CloudFormation Template here: Cloudformation Walkthrough
CloudFormation Template Overview
This CloudFormation template deploys an IAM role named SkySaverScheduler into your AWS account. The role is designed to grant the necessary permissions for your system to monitor and manage AWS resources, such as Lambda functions, EC2 instances, Auto Scaling Groups (ASGs), and RDS databases. Below are some key highlights of the template:
Key Components
IAM Role:
SkySaverScheduler- This role is created to give your system access to essential AWS services. It can assume various permissions for services such as Lambda, EC2, Auto Scaling, and RDS.
ExternalId parameter
- The template prompts you for your External ID when deploying via the CloudFormation console or CLI. Copy the value from Tenant Management > Defaults tab in the SkySaver portal and paste it into the parameter field during deployment. This ensures the trust policy condition matches your project configuration.
Permissions Overview
The template defines several policy statements to grant the required permissions for managing specific AWS services:
Lambda Permissions:
- Actions:
ListFunctions,ListTags,GetFunctionConcurrency,PutFunctionConcurrency,DeleteFunctionConcurrency, etc. - Purpose: Provides the ability to list and manage Lambda function configurations and concurrency settings.
- Actions:
EC2 Permissions:
- Actions:
StartInstances,StopInstances,DescribeInstances,ModifyInstanceAttribute. - Purpose: Enables control over EC2 instances, allowing the system to start, stop, and modify instance attributes.
- Actions:
ENI and Security Group Finder Permissions:
- Actions:
DescribeNetworkInterfaces,DescribeSecurityGroups. - Purpose: Enables the Unattached Network Interface Finder and Orphaned Security Group Finder automations to discover unattached ENIs and orphaned security groups for cleanup reporting.
- Actions:
Auto Scaling Group (ASG) Permissions:
- Actions:
DescribeAutoScalingGroups,UpdateAutoScalingGroup,DescribeTags. - Purpose: Grants the ability to manage Auto Scaling Groups, including updating configurations.
- Actions:
RDS Permissions:
- Actions:
DescribeDBClusters,StopDBCluster,StartDBCluster,ModifyDBCluster, etc. - Purpose: Enables the system to manage RDS database instances and clusters, including starting, stopping, and modifying configurations.
- Actions:
Tagging Permissions:
- Action:
tag:GetResources. - Purpose: Allows the system to retrieve resources based on their tags, helping in identifying and managing resources within the account.
- Action:
S3 Permissions (for Cost and Usage Reports):
- Actions:
ListBucket,GetObject,GetBucketLocation. - Purpose: Enables the system to read Cost and Usage Report (CUR) data from your S3 bucket for cost analysis and reporting.
- Actions:
Cost Explorer Permissions:
- Actions:
GetRightsizingRecommendation,GetCostAndUsage,GetSavingsPlansPurchaseRecommendation,GetReservationPurchaseRecommendation. - Purpose: Allows the system to retrieve cost optimization recommendations and cost data from AWS Cost Explorer to identify savings opportunities.
- Actions:
S3 Intelligent Tiering Permissions:
- Actions:
ListAllMyBuckets,GetBucketLocation,GetLifecycleConfiguration,PutLifecycleConfiguration,GetBucketTagging,PutIntelligentTieringConfiguration. - Purpose: Enables the S3 Intelligent Tiering automation to apply cost-optimized storage class configurations to your S3 buckets.
- Actions:
Trust Policy
- The
AssumeRolePolicyDocumentgrants permission for AWS account975050237171to assume theSkySaverSchedulerrole. Only resources in the skysaver account that have access to the External ID that you define in your configuration will have access to the role.